5Gセキュリティ市場 概要
MRFRの分析によると、2024年の5Gセキュリティ市場規模は28.47億米ドルと推定されています。5Gセキュリティ業界は、2025年に40.53億米ドルから2035年には1385.8億米ドルに成長すると予測されており、2025年から2035年の予測期間中に年平均成長率(CAGR)は42.36を示しています。
主要な市場動向とハイライト
5Gセキュリティ市場は、サイバーセキュリティの需要の増加と規制の圧力によって、 substantial growth の準備が整っています。
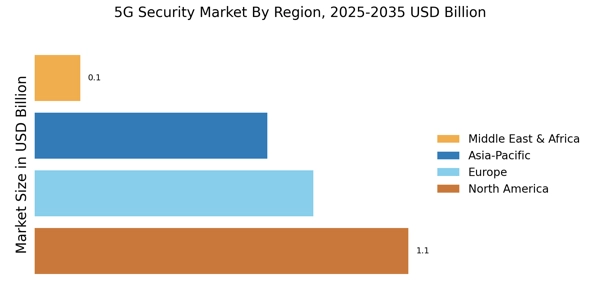
- 北米は5Gセキュリティ市場ソリューションの最大の市場であり、通信インフラへの堅実な投資を反映しています。
- アジア太平洋地域は、急速なデジタルトランスフォーメーションとIoTの採用により、最も成長が早い市場として浮上しています。
- 製造業が市場規模でリードしており、医療セグメントはセキュリティニーズの高まりにより最も急成長しています。
- サイバー脅威の増加と規制遵守の必要性が、5Gセキュリティ市場の拡大を促進する主要な要因です。
市場規模と予測
| 2024 Market Size | 2.847 (米ドル十億) |
| 2035 Market Size | 138.58 (米ドル十億) |
| CAGR (2025 - 2035) | 42.36% |
主要なプレーヤー
エリクソン(SE)、ノキア(FI)、ファーウェイ(CN)、シスコシステムズ(US)、ZTEコーポレーション(CN)、ジュニパーネットワークス(US)、チェックポイントソフトウェアテクノロジーズ(IL)、パロアルトネットワークス(US)、フォーティネット(US)