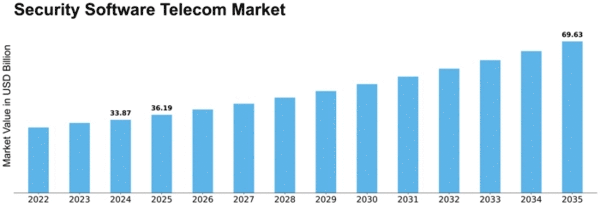
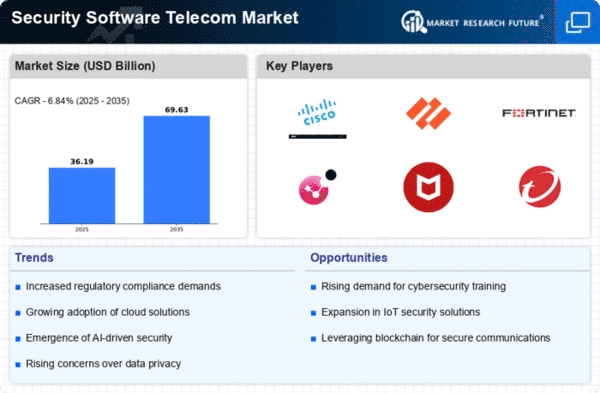
Security Software Telecom Size
Security Software Telecom Market Growth Projections and Opportunities
The telecommunications industry faces numerous security challenges, leading to a growing demand for security software solutions tailored to this sector. One significant market factor driving this demand is the escalating threat landscape. With the proliferation of cyberattacks targeting telecom networks, including Distributed Denial of Service (DDoS) attacks, data breaches, and network intrusions, there is a pressing need for robust security measures to safeguard critical infrastructure and sensitive customer data. As cyber threats become increasingly sophisticated and frequent, telecom companies are investing in advanced security software to detect, prevent, and mitigate potential security breaches.
Additionally, regulatory compliance is a crucial market factor influencing the adoption of security software in the telecom sector. Telecom companies are subject to stringent regulations and compliance requirements aimed at protecting consumer privacy, ensuring network integrity, and safeguarding against cyber threats. Regulations such as the General Data Protection Regulation (GDPR), the California Consumer Privacy Act (CCPA), and industry-specific standards like the Payment Card Industry Data Security Standard (PCI DSS) impose strict guidelines on telecom operators regarding the handling, storage, and transmission of customer data. Compliance with these regulations necessitates the implementation of robust security software solutions to maintain regulatory compliance and avoid costly penalties.
Moreover, the increasing complexity of telecom networks and the rapid evolution of technology contribute to the demand for security software in this market. Telecom networks encompass a wide range of interconnected systems, including mobile networks, fixed-line networks, cloud infrastructure, and Internet of Things (IoT) devices, creating a vast attack surface for cyber threats. As telecom companies embrace new technologies such as 5G, virtualization, and software-defined networking (SDN), they face new security challenges and vulnerabilities that require innovative security solutions to address. Security software tailored to the unique requirements of telecom networks, such as network traffic analysis, threat intelligence, and real-time monitoring, is essential to safeguarding against emerging threats and ensuring the resilience of telecom infrastructure.
Furthermore, the increasing adoption of digital services and the proliferation of connected devices drive the demand for security software in the telecom market. The rise of digital transformation initiatives, cloud-based services, and IoT deployments introduces new security risks and vulnerabilities that telecom operators must address. With the expansion of mobile banking, e-commerce, telemedicine, and other online services, telecom networks become prime targets for cybercriminals seeking to exploit vulnerabilities and compromise sensitive data. Security software solutions that provide comprehensive protection against malware, phishing attacks, and unauthorized access help telecom companies safeguard their networks and protect customer information in an increasingly digital and interconnected world.
Additionally, the competitive landscape within the telecom industry influences the adoption of security software solutions. As telecom operators compete to attract and retain customers, security has become a critical differentiator in the market. Consumers and businesses alike prioritize security when choosing telecom providers, preferring operators that demonstrate a commitment to protecting their privacy and data. Telecom companies that invest in robust security software solutions can gain a competitive edge by offering enhanced security features, proactive threat detection, and incident response capabilities, thereby strengthening customer trust and loyalty.


















Leave a Comment