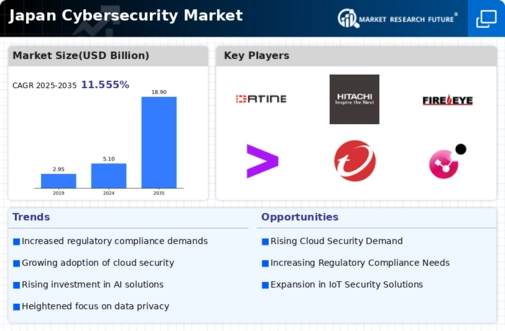
Japan Cybersecurity Market
ID: MRFR/ICT/44357-HCR
200 Pages
Nirmit Biswas
Last Updated: April 06, 2026
Japan Cybersecurity Market Size, Share and Trends Analysis Report By Solution (IdentityAccess Management, RiskCompliance Management, Unified Threat Management, Disaster Recovery, Firewall, Antivirus, Web Filtering, Data Loss Prevention, Security Information and Event Management, Others), By Services (Managed Services, Professional Services), By Professional Services (TrainingEducation, Consulting, SupportMaintenance, DesignIntegration), By Security Type (Network Security, End Point Security, Application Security, Cloud Security, Wireless Security, Others), By Deployment (Cloud, On-Premise), By Organization Size (SmallMedium Enterprise, Large Enterprise) andBy Vertical (Manufacturing, Banking, Financial Services, and Insurance (BFSI), Healthcare, ITTelecommunication, Retail, Government, AerospaceDefense, Others)- Forecast to 2035