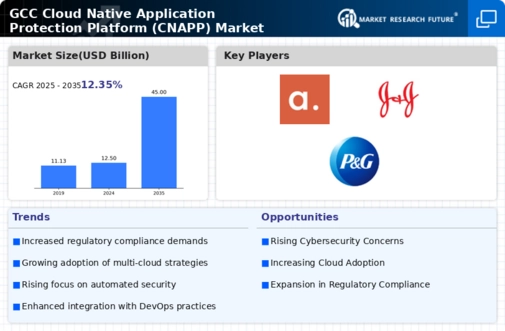
GCC Information and Communications Technology Market Segmentation
Information and Communications Technology By Application (USD Billion, 2026-2035)
- Security Monitoring
- Threat Detection
- Compliance Management
- Vulnerability Management
Information and Communications Technology By Deployment Model (USD Billion, 2026-2035)
- Public Cloud
- Private Cloud
- Hybrid Cloud
Information and Communications Technology By End User (USD Billion, 2026-2035)
- Large Enterprises
- Small and Medium Enterprises
- Government Organizations
Information and Communications Technology By Service Type (USD Billion, 2026-2035)
- Managed Services
- Professional Services
- Consulting Services
Information and Communications Technology By Technology (USD Billion, 2026-2035)
- Container Security
- Serverless Security
- API Security