Qualitative and quantitative insights were obtained by interviewing supply-side and demand-side stakeholders during the primary research process. CEOs, CTOs, VPs of Product Development, Chief Information Security Officers (CISOs), and Heads of Data Governance from data concealing solution vendors, cloud service providers, and cybersecurity OEMs comprised supply-side sources. Demand-side sources of information included Chief Information Officers (CIOs), Data Protection Officers (DPOs), Enterprise Architects, IT Security Directors, and Compliance Leads from healthcare organizations, retail enterprises, government agencies, and BFSI institutions. Market segmentation was validated across software and services components, cloud deployment timelines were confirmed, and insights on enterprise adoption patterns, pricing models, and integration dynamics with existing data governance frameworks were gathered using primary research.
Primary Respondent Breakdown:
By Designation: C-level Primaries (32%), Director Level (30%), Others (38%)
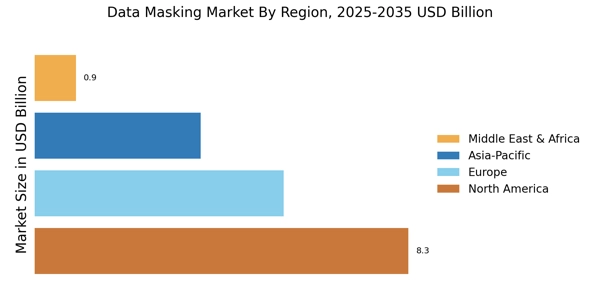
By Region: North America (38%), Europe (25%), Asia-Pacific (28%), Rest of World (9%)
Revenue mapping and deployment volume analysis were implemented to determine global market valuation. The methodology comprised the following:
Identification of over 50 key vendors in North America, Europe, Asia-Pacific, and Latin America who specialize in data masking software and related services
Product mapping for professional services, managed security services, static data masking, and dynamic data masking
Examination of annual revenues that are specific to data privacy and obfuscation solution portfolios, as reported and modeled
In 2024, the coverage of vendors will account for 75-80% of the global market share.
Derive segment-specific valuations across business functions, including HR, sales & marketing, and legal finance operations, through extrapolation using bottom-up (enterprise deployment volume × Average Selling Price by organization size and region) and top-down (vendor revenue validation against total IT security spending) approaches.