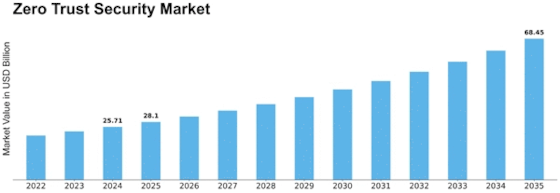
Zero Trust Security Size
Zero Trust Security Market Growth Projections and Opportunities
Zero Trust Security is a rapidly growing market, with businesses recognizing the need for robust security measures in today's digital landscape. As organizations increasingly rely on cloud-based services and remote work, the traditional perimeter-based security approach is no longer sufficient. In this highly competitive market, companies are employing various market share positioning strategies to stand out from the crowd.
One of the strategies commonly used is product differentiation. Zero Trust Security vendors strive to develop unique features and capabilities that set them apart from their competitors. By offering innovative solutions that address specific security challenges, companies can position themselves as industry leaders. This could include advanced threat detection algorithms, machine learning capabilities, or seamless integration with existing security infrastructure.
Another key approach is focused on target market segmentation. Zero Trust Security providers identify specific industries or sectors that are most susceptible to cyber threats and tailor their offerings accordingly. For example, they might develop specialized solutions for the healthcare sector, financial institutions, or government agencies. By understanding the unique security needs of different industries, companies can effectively position themselves as experts in their respective fields.
Price positioning is also crucial in the Zero Trust Security market. Some companies choose to compete on price, offering affordable solutions to attract cost-conscious customers. This approach can be effective in gaining market share, especially in price-sensitive industries. On the other hand, some vendors position themselves as premium providers, offering high-end security solutions that come with a higher price tag. This strategy appeals to customers who prioritize top-notch security and are willing to invest in cutting-edge technology.
Partnerships and collaborations are another market share positioning strategy employed by Zero Trust Security vendors. By teaming up with other industry leaders or integrating their solutions with popular platforms, companies can expand their reach and credibility. For example, partnering with cloud service providers or network infrastructure companies can help Zero Trust Security vendors gain access to a larger customer base and enhance their market position.
Finally, effective marketing and branding play a crucial role in market share positioning. Zero Trust Security vendors invest in creating compelling marketing campaigns that highlight the value and benefits of their solutions. This includes thought leadership articles, case studies, and testimonials that demonstrate their expertise and success in protecting organizations from cyber threats. By building a strong brand reputation, companies can differentiate themselves from competitors and establish themselves as trusted security providers.



















Leave a Comment