US Food, Beverages & Nutrition Market Segmentation
Food, Beverages & Nutrition By Type (USD Billion, 2025-2035)
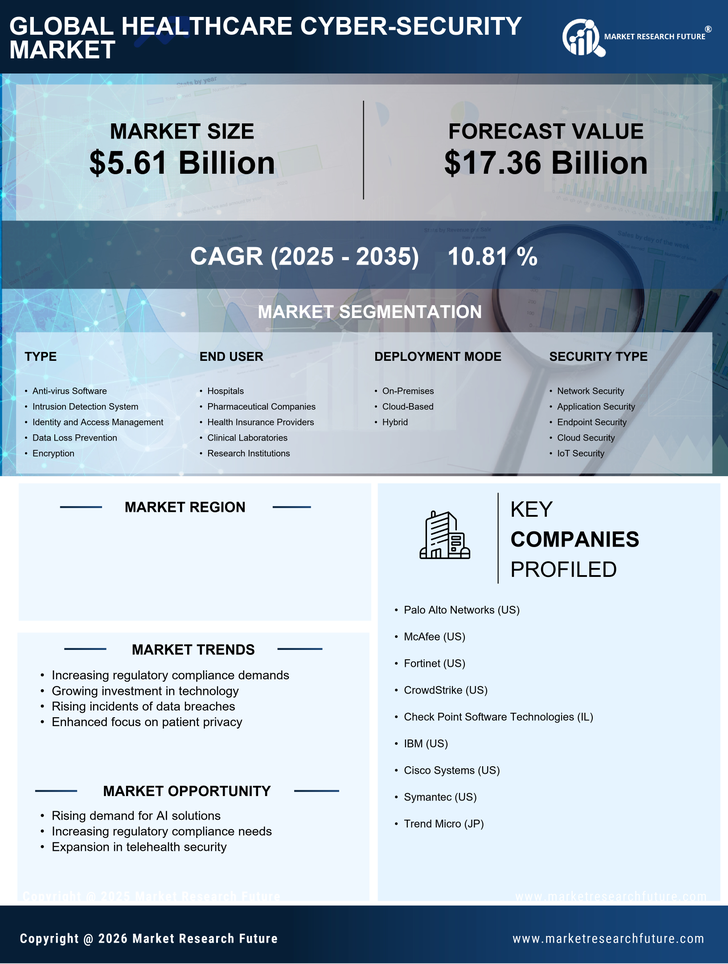
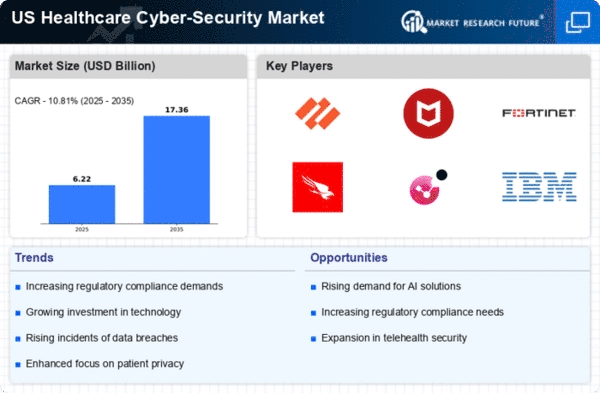
- Anti-virus Software
- Intrusion Detection System
- Identity and Access Management
- Data Loss Prevention
- Encryption
Food, Beverages & Nutrition By End User (USD Billion, 2025-2035)
- Hospitals
- Pharmaceutical Companies
- Health Insurance Providers
- Clinical Laboratories
- Research Institutions
Food, Beverages & Nutrition By Deployment Mode (USD Billion, 2025-2035)
- On-Premises
- Cloud-Based
- Hybrid
Food, Beverages & Nutrition By Security Type (USD Billion, 2025-2035)
- Network Security
- Application Security
- Endpoint Security
- Cloud Security
- IoT Security