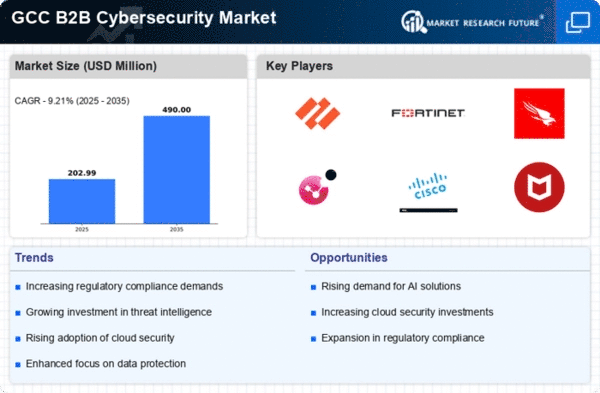
GCC B2B Cybersecurity Market
ID: MRFR/ICT/57231-HCR
200 Pages
Kiran Jinkalwad
Last Updated: April 06, 2026
GCC B2B Cybersecurity Market Research Report By Offering (Solution, Services), By Security Type (Network Security, End Point Security, Email Security, Deception Technology, Application Technology, Wireless Security, Others), By Deployment Type (On-Cloud, On-Premises), By Organization Size (Freelancers or Micro-Organizations, SME's, Large Organizations) and By Industry Vertical (BFSI, Manufacturing, Healthcare, Retail, IT & Telecommunications, Aerospace & Defense, Government, Others) - Forecast to 2035