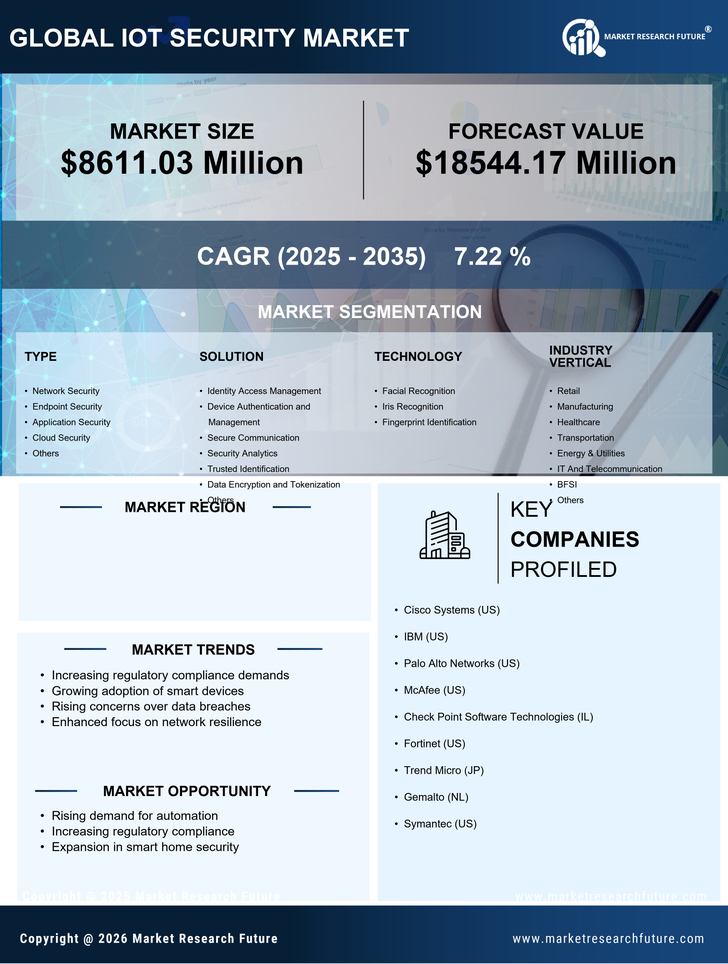
US Information and Communications Technology Market Segmentation
Information and Communications Technology By Type (USD Million, 2025-2035)
- Network Security
- Endpoint Security
- Application Security
- Cloud Security
- Others
Information and Communications Technology By Solution (USD Million, 2025-2035)
- Identity Access Management
- Device Authentication and Management
- Secure Communication
- Security Analytics
- Trusted Identification
- Data Encryption and Tokenization
- Others
Information and Communications Technology By Technology (USD Million, 2025-2035)
- Facial Recognition
- Iris Recognition
- Fingerprint Identification
Information and Communications Technology By Industry Vertical (USD Million, 2025-2035)
- Retail
- Manufacturing
- Healthcare
- Transportation
- Energy & Utilities
- IT And Telecommunication
- BFSI
- Others