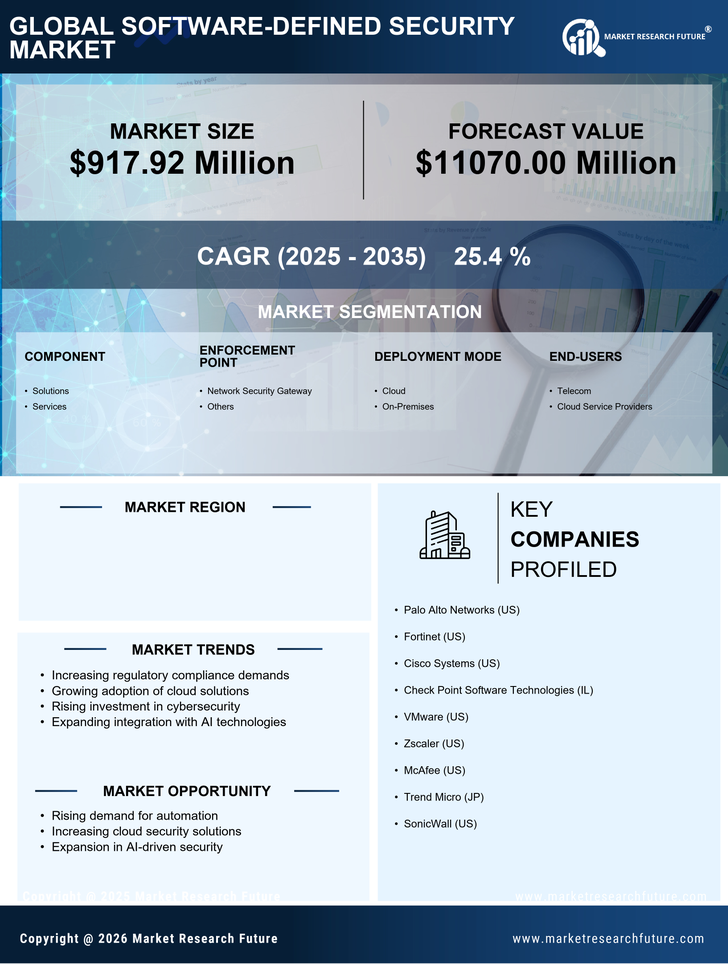
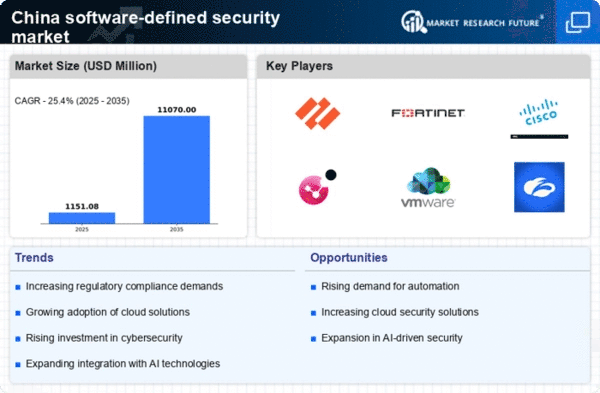
China Information and Communications Technology Market Segmentation
Information and Communications Technology By Component (USD Million, 2025-2035)
- Solutions
- Services
Information and Communications Technology By Enforcement Point (USD Million, 2025-2035)
- Network Security Gateway
- Others
Information and Communications Technology By Deployment Mode (USD Million, 2025-2035)
- Cloud
- On-Premises
Information and Communications Technology By End-Users (USD Million, 2025-2035)
- Telecom
- Cloud Service Providers