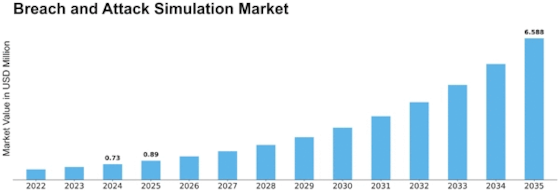
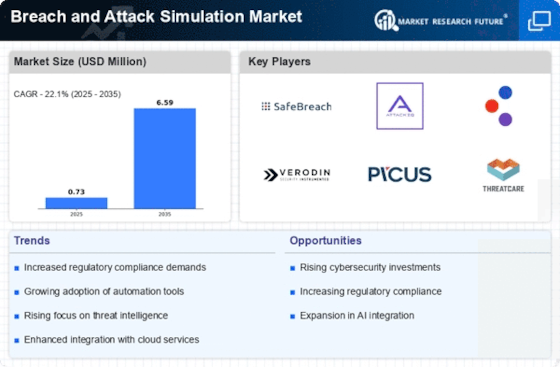
Breach Attack Simulation Size
Breach Attack Simulation Market Growth Projections and Opportunities
The market for breach and attack simulation is driven by several factors that highlight how crucial cybersecurity is becoming in today's digital environment. The increasing frequency and effectiveness of cyber threats is a major driver propelling the developing of the BAS market.The increased need for sophisticated cybersecurity solutions because of this knowledge has seen BAS emerge as a vital tool for businesses looking to improve their cyber resilience. Strong cybersecurity procedures, such as frequent security testing and cyberthreat simulation, are required by the legislation. Because of this, companies are forced to spend money on BAS solutions to abide by legal requirements and strengthen their defenses against possible violations.
The BAS market is expanding because of this regulatory-driven need, especially as non-compliance can result in significant financial penalties and harm to one's reputation. The dynamic expansion of the BAS industry is partly attributed to the increasing nature of cyber threats. Organizations need to keep ahead of the curve in terms of their cybersecurity posture since attackers are always implementing new strategies and taking advantage of undiscovered weaknesses. By mimicking actual intrusions, BAS solutions offer a proactive strategy that helps businesses find gaps in their security architecture and put in place the required defenses. Because of their flexibility and agility, BAS systems are essential for companies trying to maintain their resilience regardless of a constantly shifting threat scenario.
Furthermore, the demand for BAS solutions is fueled by the growing digitization of enterprises and the broad adoption of cloud technologies; as businesses embrace digital change, the attack surface increases, opening new points of entry for potential cyberattacks. The adoption of cloud-based architectures and remote work arrangements has resulted in an increased demand for thorough cybersecurity protocols. BAS solutions give enterprises a comprehensive picture of their protection stance by simulating assaults across several settings and protecting physical and cloud-based assets. The market is expanding in part due to organizations' increasing knowledge of the profitability of preventive cybersecurity measures.
By putting money into BAS solutions, businesses may proactively find and fix vulnerabilities, decreasing the chance of costly data theft and the ensuing damage to their finances and reputation. With companies realizing the benefits of proactive cybersecurity measures in the long run, the BAS market is expected to rise steadily.


















Leave a Comment