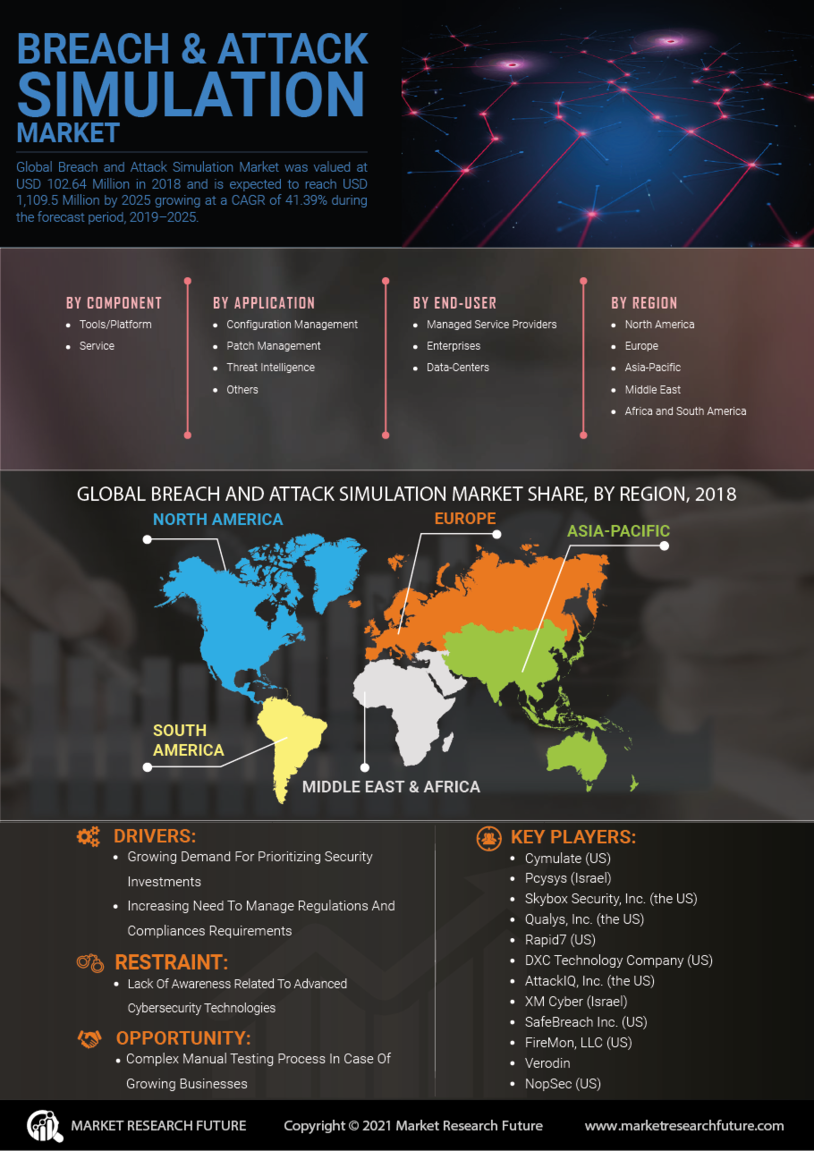
Information and Communications Technology Market Segmentation
Information and Communications Technology By Offering (USD Million, 2025-2035)
- Tools and platform
- Services
- On-demand analysts
Information and Communications Technology By Deployment Mode (USD Million, 2025-2035)
- On-premise
- Cloud
Information and Communications Technology By Application (USD Million, 2025-2035)
- Patch management
- Threat management
- Configuration management
- Compliance and control management
Information and Communications Technology By End-User (USD Million, 2025-2035)
- Manage and service providers
- Data centres and enterprises