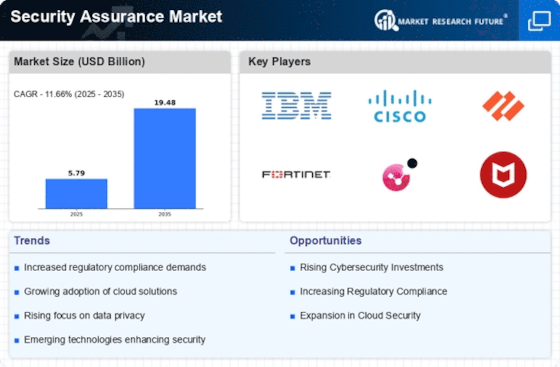
Top Industry Leaders in the Security Assurance Market
Competitive Landscape of the Security Assurance Market
The digital landscape is evolving at breakneck speed, and with it, the threats to data security become increasingly sophisticated. This vast and dynamic market is home to a diverse range of established and emerging players, all vying for their piece of the pie.
Key Players:
- Avaya Inc.(US)
- IBM Corporation (US)
- Infosys Limited (India)
- Micro Focus (UK)
- NETSCOUT (US)
- SAS Institute Inc. (US)
- Capgemini (France)
- Spirent Communications (UK)
- Radix Security Inc. (Israel)
- Tenable Inc. (US)
- Telos Corporation (US)
- Happiest Minds (India)
- CIPHER Security LLC (US)
- BizCarta Technologies India Pvt Ltd
- Aura Information Security (Australia)
Factors for Market Share Analysis:
- Product Portfolio Breadth and Depth: The ability to offer a wide range of services across vulnerability assessments, penetration testing, compliance management, threat detection, and incident response holds significant weight.
- Technological Innovation: Investing in cutting-edge AI, automation, and cloud-based solutions is crucial for staying ahead of evolving threats and offering efficient security assurance.
- Geographic Reach and Scalability: Global presence and the ability to cater to diverse regional needs are key differentiators, especially for large enterprises with complex security requirements.
- Industry Expertise and Specialization: Focusing on specific industry verticals allows for tailored solutions, deeper understanding of regulatory landscapes, and building trust with niche clientele.
- Pricing Strategies and Customer Service: Flexible pricing models, subscription options, and exceptional customer support play a vital role in attracting and retaining clients.
New and Emerging Companies:
- Start-ups focused on niche security domains: Companies like Vectra Networks (AI-powered network detection and response) and CyberArk (privileged access management) are rapidly gaining traction by addressing specific security concerns with innovative solutions.
- Open-source security platforms: Tools like Nessus and Metasploit are democratizing security assurance by offering cost-effective vulnerability assessment and penetration testing capabilities, especially for smaller businesses.
- Security Service Providers (SSPs): Managed Security Service Providers (MSSPs) and Security Information and Event Management (SIEM) providers like LogRhythm and Splunk are integrating security assurance as part of their broader security service offerings, creating one-stop solutions for enterprises.
Current Company Investment Trends:
- Cloud-based security assurance platforms: Leading players are heavily investing in cloud-based solutions for greater scalability, improved threat detection accuracy, and real-time data analysis capabilities.
- Integration with AI and automation: Automating routine tasks and leveraging AI for threat detection and incident response is a major focus area, aiming for faster response times and improved efficiency.
- Compliance-focused solutions: With the ever-evolving regulatory landscape, companies are investing in solutions that help organizations comply with industry-specific and regional data privacy regulations.
- Partnerships and acquisitions: Collaborations with smaller security-focused firms and acquisitions of niche technology providers are common strategies for expanding capabilities and entering new markets.
Latest Company Updates:
Jan 5, 2024: Rapid7, a security assurance leader, has acquired SecMonSec, a cloud-based vulnerability management platform provider. This move enhances Rapid7's existing vulnerability management capabilities and expands its cloud-based offerings. Analysts predict this acquisition to further solidify Rapid7's position in the competitive market.
Jan 4, 2024: Palo Alto Networks has announced a strategic partnership with Crowdstrike, another major security assurance player. This partnership combines Palo Alto's Cortex XDR (Extended Detection and Response) platform with Crowdstrike's Falcon XDR, creating a comprehensive solution for threat detection, investigation, and response. Experts expect this collaboration to disrupt the XDR market and offer enterprises a more robust security posture.
Jan 3, 2024: Mandiant, a renowned cybersecurity consultant, has launched a new incident response and forensic investigation lab in Singapore. This expansion strengthens Mandiant's presence in the Asia-Pacific region and caters to the growing demand for its services in the rapidly evolving APAC threat landscape.
Dec 22, 2023: Tenable Holdings, a leading vulnerability management vendor, has acquired Nessus, the popular open-source vulnerability scanner. This acquisition brings together Tenable's commercial solutions with Nessus' broad user base and open-source expertise, potentially opening doors for wider security assurance adoption.