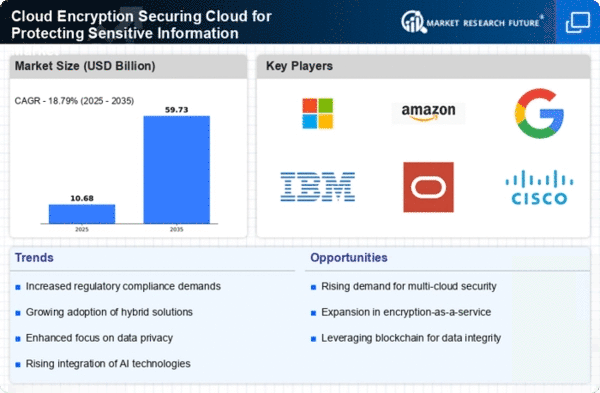
Information and Communications Technology Market Segmentation
Information and Communications Technology By Application (USD Billion, 2025-2035)
- Data Encryption
- File Encryption
- Database Encryption
- Network Encryption
- Application Encryption
Information and Communications Technology By Deployment Model (USD Billion, 2025-2035)
- Public Cloud
- Private Cloud
- Hybrid Cloud
- Community Cloud
Information and Communications Technology By End User (USD Billion, 2025-2035)
- Government
- Healthcare
- Financial Services
- Retail
- Telecommunications
Information and Communications Technology By Encryption Type (USD Billion, 2025-2035)
- Symmetric Encryption
- Asymmetric Encryption
- Hashing
- Tokenization
Information and Communications Technology By Compliance Standards (USD Billion, 2025-2035)
- General Data Protection Regulation
- Health Insurance Portability and Accountability Act
- Federal Information Processing Standards
- Payment Card Industry Data Security Standard